توضیحات
ABSTRACT
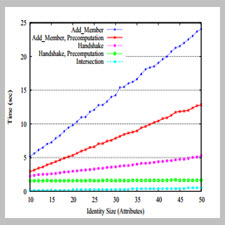
The need for communication privacy over public networks is of growing concern in today’s society. As a result, privacy-preserving authentication and key exchange protocols have become critical primitives in building secure distributed systems. Secret handshakes provide such a service by allowing two members of the same group to secretly and privately authenticate to each other and agree on a shared key for further communication. This paper presents the first efficient secret handshake schemes with unlinkable, reusable credentials that do not rely on random oracles for their security (solving open problems from prior literature). In previous work, secret handshakes were extended with roles, so that a group member A can specify the role another group member B must have in order to successfully complete the protocol with A. We generalize the traditional and role-based secret handshake in two ways. First, we present a secret handshake with dynamic matching, in which each party can specify both the group and the role the other must have in order to complete the handshake. Second, we provide a novel extension of secret handshakes to include attributes, allowing the handshake to be based on approximate (or fuzzy) matching. We demonstrate the practicality and efficiency of our protocols by evaluating a prototype implementation. We integrate our dynamic matching protocol into IPsec, and we detail the performance tradeoffs associated with our fuzzy matching scheme. Our experiments indicate that our solutions offer attractive performance.
INTRODUCTION
A secret handshake scheme, introduced by Balfanz et al. [5], allows two members of the same group to secretly authenticate to each other and agree on a shared key for further communication. Such authentication is privacy preserving, meaning that if the participants belong to the same
group, they only learn that they are members of that group (without learning each other’s identities), and learn nothing about each other otherwise. The most commonly used example of such interaction is the mutual authentication of CIA agents. That is, consider a CIA agent who wants to authenticate to another agent but does not want to reveal his credentials to anyone other than CIA agents. Obviously, two CIA agents should be able to successfully complete the handshake, and other parties should not be able to perform or recognize the handshake. Such schemes can also be used by members of secret societies to identify other members, by the military to discover and use a secret service, etc.
Year: 2007
Publisher : NSF
By : Giuseppe Ateniese, Marina Blanton, Jonathan Kirsch
File Information: English Language/ 19 Page / size: 251 KB
Download: click
سال : 2007
ناشر : NSF
کاری از : Giuseppe Ateniese, Marina Blanton, Jonathan Kirsch
اطلاعات فایل : زبان انگلیسی / 19 صفحه / حجم : KB 251
لینک دانلود : روی همین لینک کلیک کنید








نقد و بررسیها
هنوز بررسیای ثبت نشده است.