توضیحات
ABSTRACT
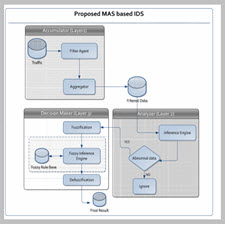
This paper presents an Intrusion Detection System (IDS) with the integration of multi agent systems and artificial intelligence techniques such as fuzzy logic controller (FLC), multi-layer perceptron (MLP) and adaptive neurofuzzy inference system (ANFIS). The paper introduces Network Intrusion Detection Systems (NIDS), which monitors the network traffic and detect any possible attacks. The system is made up of three agents: accumulator, analyser and decision maker agents. The accumulator agent works to gather and filter network traffics. The analyser agent uses decision tree (DT) to classify the data. Finally, the decision maker agent uses fuzzy logic controller (FLC) to make the final decision. The proposed system was simulated using KDDCup 1999 dataset and the experimental results show an improvement of the attack detection accuracy to 99.95% and false alarm rate of 1%.
INTRODUCTION
An Intrusion Detection System (IDS) is a security tool used to detect intrusion. In comparison, security systems such as firewalls and cryptography are security mechanisms help to secure organisation in different ways (i.e. blocking unauthorised traffic and hide information). An Intrusion Detection System or similar systems (e.g. Intrusion Prevention System or Intrusion Response System) monitor network traffic to analyze them in order to detect attacks [1]. There are two types of IDS: host and network based IDSs [2]. Host-based IDS (HIDS) monitors and analyses events pertaining to the operating system process such as system calls and processes ID. On the contrary, network-based IDS (NIDS) monitors and analyses network traffic. With heavy use of Internet, it becomes crucial to protect the organizations against the immense number of possible attacks. As such, NIDS has become more important than HIDS. There are two type of detection approach: signature and anomaly [2]. The signature-based detection (i.e. misuse based) uses defined signatures to detect malicious traffic by analysing the network flow [2].The anomaly detection detects attacks by estimating the normal behaviour and any deviation from it is observer that exceeds predefined threshold is considered malicious [2].
Year: 2013
Publisher : Springer
By : Ali Feizollah, Shahaboddin Shamshirband, Nor Badrul Anuar,Rosli Salleh, and Miss Laiha Mat Kiah
File Information: English Language/ 12 Page / size: 813 KB
Download: click
سال : 2013
ناشر : Springer
کاری از : Ali Feizollah, Shahaboddin Shamshirband, Nor Badrul Anuar,Rosli Salleh, and Miss Laiha Mat Kiah
اطلاعات فایل : زبان انگلیسی / 12 صفحه / حجم : KB 813
لینک دانلود : روی همین لینک کلیک کنید








نقد و بررسیها
هنوز بررسیای ثبت نشده است.