توضیحات
ABSTRACT
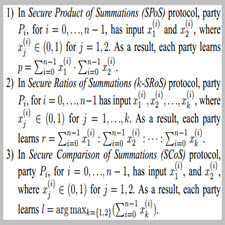
In privacy-preserving data mining, a number of parties would like to jointly learn a function of their private data sets in a way that no information about their inputs, beyond the output itself, is revealed as a result of such computation. Yang et al. 2010 showed that several popular data mining algorithms can be reduced to three basic operations, secure implementation of which – termed Secure Product of Summations (SPoS), Secure Ratios of Summations (SRoS), and Secure Comparison of Summations (SCoS) – would lead to privacy- preserving data mining solutions. The authors showed that prior privacy-preserving data mining solutions are unsatisfactory in presence of participants’ collusion and they gave new mplementation of these operations that were designed to sustain the collusion. In this work, we show that unfortunately the protocols of Yang et al. leak a significant amount of private information and are not secure even if no collusion takes place. We then show how these operations can be securely and efficiently realized in the same and stronger security models, which leads to fully secure solutions for many data mining algorithms.
INTRODUCTION
Privacy-preserving data mining has received a significant amount of attention in the research literature in the recent years. This is not surprising given a vast growth of the amount of collected information, including sensitive data, that we might desire to analyze. In privacy-preserving data mining, the data are distributed across multiple sites and are considered private information. The data owners would like to mine on their collective data, but in a way that no information about their private data sets is available to other participants (except what can be deduced from the output of the computation). In this distributed setting, we can distinguish between horizontally partitioned data, vertically partitioned data, and their hybrid. In horizontally partitioned data, each data owner has complete information about a distinct set of entities. In vertically partitioned data, on the other hand, all parties hold information about the same set of entities, but each possesses information about distinct attributes
Year : 2011
Publisher : Department of Computer Science and Engineering University of Notre Dame
By : Marina Blanton
File Information : English Language/ 10Page / size:160KB
Download : click
سال : 2011
ناشر : Department of Computer Science and Engineering University of Notre Dame
کاری از : Marina Blanton
اطلاعات فایل : زبان انگلیسی / 10صفحه / حجم : 160KB
لینک دانلود : روی همین لینک کلیک کنید








نقد و بررسیها
هنوز بررسیای ثبت نشده است.